Predatory publishing is a growing threat in academic research. It impacts both early-career and experienced researchers. These journals use deceptive tactics to attract submissions.
They exploit urgency, especially when researchers face deadlines for promotions, grants, or thesis defense.
The danger is real. Many researchers lose money, credibility, and their publication records.
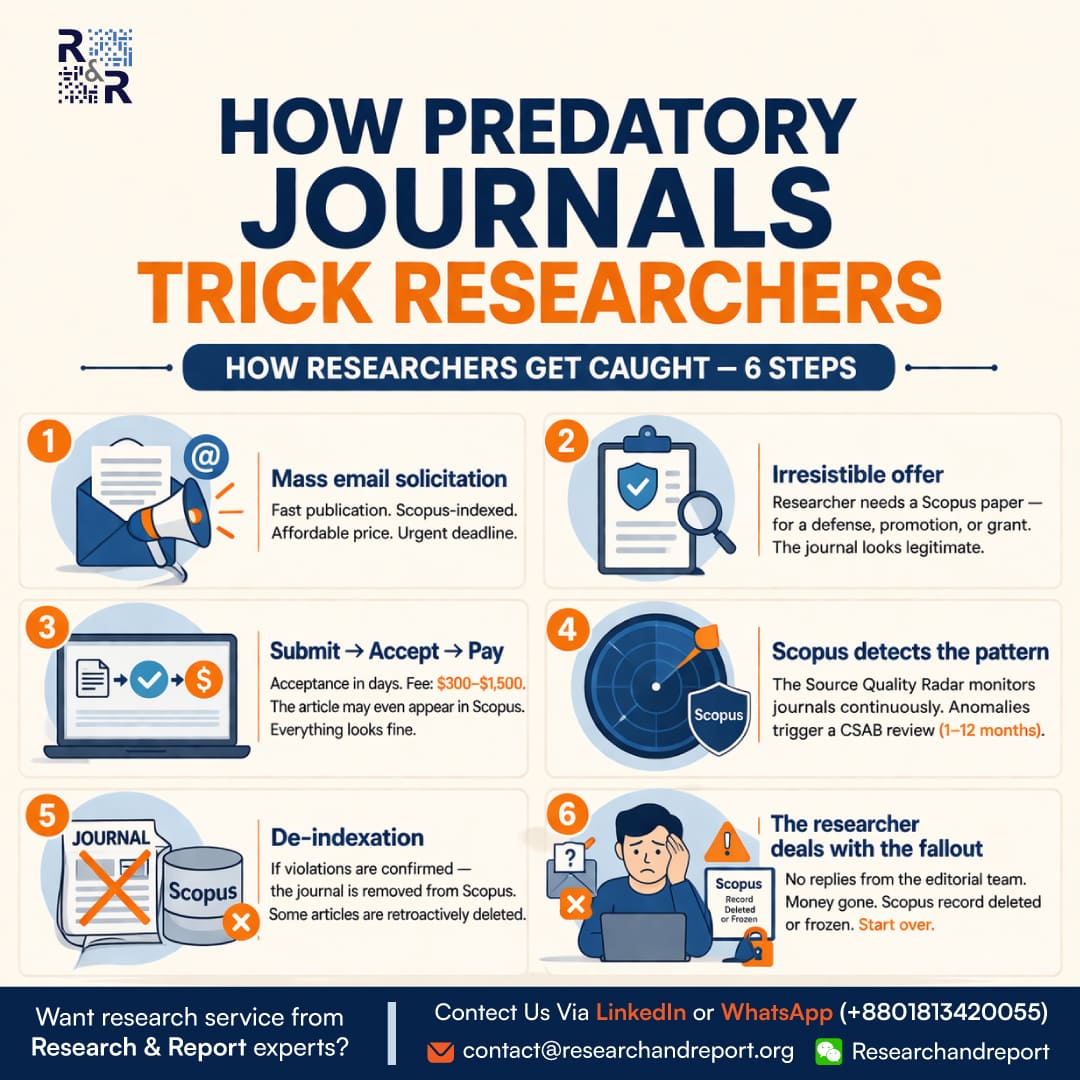
How Predatory Journals Operate
Predatory journals follow a predictable pattern. Understanding it helps you avoid costly mistakes.
The 6-Step Trap
- Mass Email Solicitation
- Personalized invitations
- Promises of fast publication
- Claims of Scopus indexing
- Irresistible Offer
- Appeals to urgency
- Targets career pressure
- Mimics legitimate journals
- Submit → Accept → Pay
- Acceptance within days
- Fees range from $300–$1,500
- Minimal or no peer review
- Monitoring Phase
- Indexing databases detect anomalies
- Suspicious patterns trigger review
- De-indexation
- Journal removed from databases
- Articles may disappear
- Researcher Fallout
- No editorial response
- Financial loss
- Academic damage
The Hidden Risk Window
There is a critical delay between misconduct and detection.
👉 This gap can last 1–12 months
During this time:
- Journals still appear indexed
- Researchers trust the system
- Thousands submit papers
Why Researchers Fall Into the Trap
Key Psychological Triggers
- Urgency (deadlines, promotions)
- Fear of rejection
- Lack of awareness
- Pressure to publish
Systemic Issues
- No real-time warning system
- Limited institutional guidance
- Complex indexing verification
Real-World Impact
Predatory publishing affects academic integrity globally.
Key Statistics
- Over 15,000 predatory journals identified globally
- Millions of dollars lost annually
- Thousands of papers removed after de-indexation
(Source: COPE, DOAJ, Cabell’s Reports)
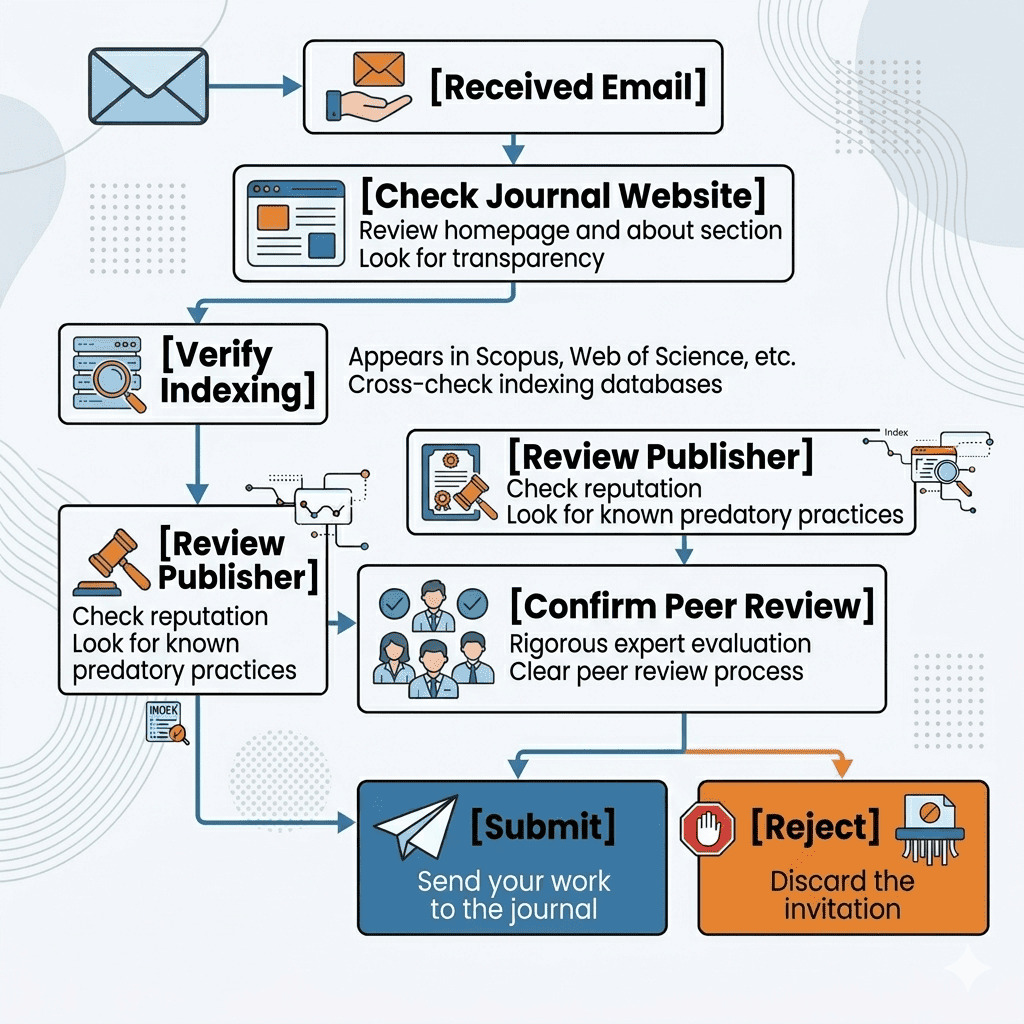
How to Identify Predatory Journals
Red Flags Checklist
- Unrealistic publication timelines
- Aggressive email invitations
- Fake indexing claims
- Poor website quality
- Lack of peer-review transparency
How to Protect Yourself
Best Practices
- Verify indexing on official databases
- Check journal history and publisher reputation
- Review editorial board credibility
- Avoid “too good to be true” offers
Data Insight: Researcher Risk Distribution (Chart)

Predatory journals are evolving. They no longer target only inexperienced researchers.
They target anyone under pressure.
The responsibility lies with researchers to verify before submitting.
Stay cautious. Publish ethically. Protect your academic reputation.
Have you ever received suspicious journal invitations? How did you verify them before submission?
References
- Committee on Publication Ethics (COPE): https://publicationethics.org
- Directory of Open Access Journals (DOAJ): https://doaj.org
- Scopus Source List: https://www.scopus.com/sources
- Cabell’s Predatory Reports: https://www2.cabells.com
- Think. Check. Submit.: https://thinkchecksubmit.org
Want research service from Research & Report experts? Please get in touch with us.